Date: 2024-07-24 05:00 | Source: techcrunch.com
Summary:
Exoticca’s platform integrates flights, hotels, meals, transfers, transportation, and local companies at travel destinations.
Main Points:
- Integrates flights, hotels, meals, and transfers.
- Connects transportation services at destinations.
- Partners with local companies.
Key Takeaways:
- Comprehensive travel service integration.
- Local partnerships enhance travel experiences.
- Simplifies travel planning and logistics.
Date: 2024-07-24 04:00 | Source: blog.cloudflare.com
Summary:
Cloudflare collaborates with Meta to launch Workers AI support for Llama 3.1.
Main Points:
- Cloudflare partners with Meta.
- Introduction of Workers AI support.
- Focus on Llama 3.1.
Key Takeaways:
- Collaboration aims to enhance AI capabilities.
- Llama 3.1 is the key focus of this support.
- Partnership highlights Cloudflare's commitment to AI advancements.
Date: 2024-07-24 03:47 | Source: Cisco

Summary:
Rodney discusses key technology trends in AI, advanced connectivity, and cybersecurity for BT in the APJC and Middle East Africa regions.
Main Points:
- AI integration is essential for predictive analytics and intelligence across platforms.
- Advanced connectivity focuses on secure networking and multicloud environments.
- Cybersecurity is crucial for protecting customer data in both on-prem and off-prem solutions.
Key Takeaways:
- AI is becoming integral in network operations and data intelligence.
- Secure connectivity is vital for cloud adoption and digital transformation.
- Robust cybersecurity measures are necessary to safeguard customer data.
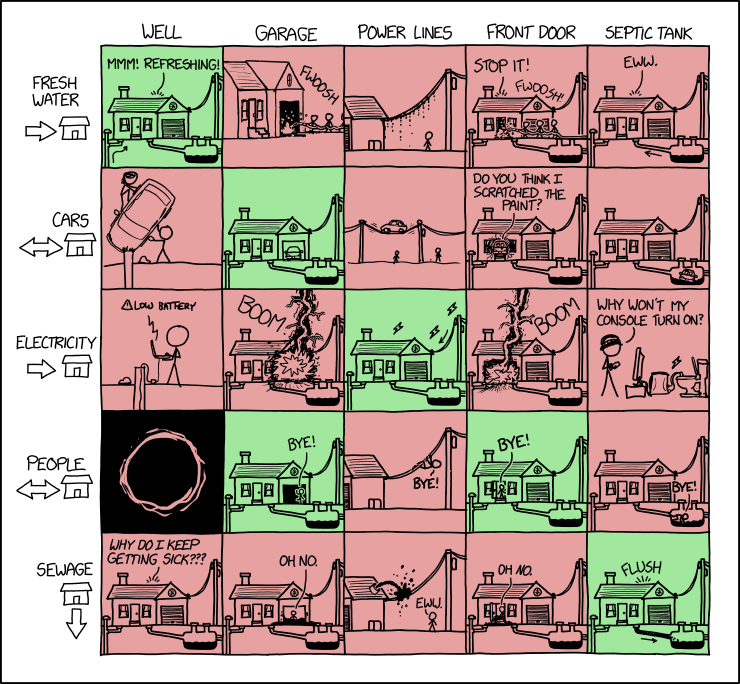
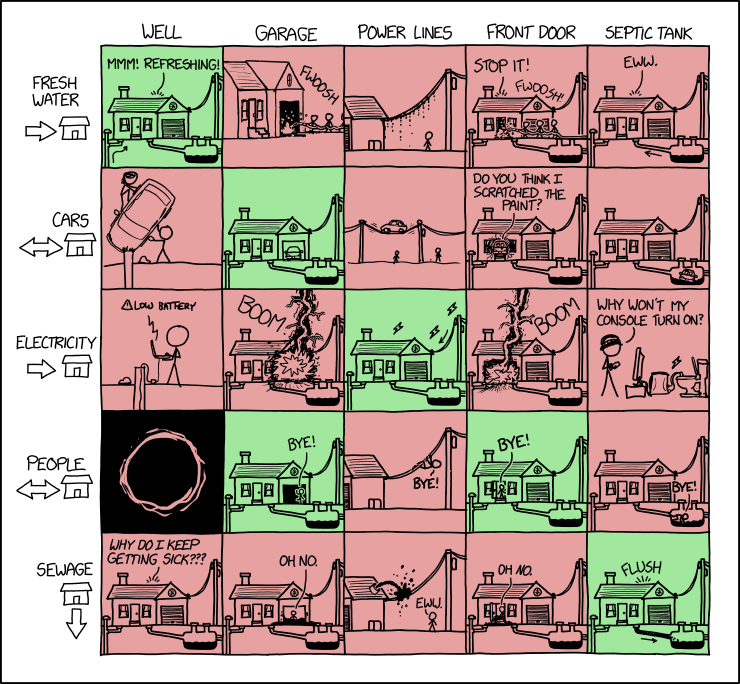
Date: 2024-07-24 00:00 | Source: xkcd.com
Date: 2024-07-23 23:50 | Source: techcrunch.com
Summary:
Elon Musk announces Tesla's robotaxi prototype reveal on October 10, alongside unspecified additional reveals, after delaying the August 8 event.
Main Points:
- Tesla's robotaxi prototype will be showcased on October 10.
- The initial reveal date was postponed from August 8.
- Other unspecified items will also be revealed at the event.
Key Takeaways:
- Tesla is preparing to unveil new technology, including a robotaxi prototype.
- The company rescheduled the robotaxi reveal from August to October.
- Additional, undisclosed items will be part of the October event.
Date: 2024-07-23 21:52 | Source: techcrunch.com
Summary:
Elon Musk announces Tesla will unveil a purpose-built "robotaxi" prototype and other unspecified items during an event on October 10.
Main Points:
- Elon Musk will showcase Tesla's "robotaxi" prototype on October 10.
- The reveal was rescheduled from August 8.
- Additional unspecified items will also be shown.
Key Takeaways:
- The "robotaxi" prototype is a key highlight of the upcoming event.
- The event date has been changed to October 10.
- There are other undisclosed items that will be revealed.
Date: 2024-07-23 21:48 | Source: blog.apnic.net
Summary:
Researchers developed 'HitchHiking,' an open-source methodology for conducting the largest Low Earth Orbit (LEO) network measurement to date.
Main Points:
- 'HitchHiking' is an open-source methodology.
- It enables the largest LEO network measurement ever conducted.
- Developed by researchers to advance network measurement techniques.
Key Takeaways:
- 'HitchHiking' offers a new approach to measuring LEO networks.
- Open-source nature allows for widespread adoption and collaboration.
- Potential to significantly impact future network measurement research.
Date: 2024-07-23 21:01 | Source: arstechnica.com
Summary:
WSJ report reveals Amazon Devices faces internal struggles and uses vague metrics to measure success.
Main Points:
- Amazon Devices uses unclear metrics to gauge performance.
- Internal conflicts are affecting Amazon Devices' operations.
- The report questions the effectiveness of Amazon Devices' strategies.
Key Takeaways:
- Vague metrics can undermine organizational success.
- Internal harmony is crucial for operational effectiveness.
- Clear strategies and goals are essential for evaluating performance.
Date: 2024-07-23 20:01 | Source: arstechnica.com
Summary:
Mark Zuckerberg advocates for open source AI but misuses the term in his statement.
Main Points:
- Mark Zuckerberg supports open source AI.
- He misuses the term "open source."
- The statement highlights a common misunderstanding.
Key Takeaways:
- Open source AI has influential proponents like Zuckerberg.
- Misunderstanding of technical terms can affect public discourse.
- Clear definitions are crucial in technology discussions.
Date: 2024-07-23 19:34 | Source: arstechnica.com
Summary:
The EPA's strategy to reduce carbon emissions from power plants has been approved for implementation.
Main Points:
- The EPA has developed a plan to cut carbon emissions.
- The plan targets power plants specifically.
- The implementation of this plan has been authorized.
Key Takeaways:
- The EPA's initiative focuses on reducing environmental impact from power plants.
- Approval of the plan marks a significant step in carbon emission control.
- Regulatory backing ensures the plan's execution and potential environmental benefits.
Date: 2024-07-23 18:53 | Source: TheAIGRID

Summary:
Meta's release of Llama 3.1, a 405 billion parameter model, includes improved performance, expanded context windows, and enhanced reasoning capabilities.
Main Points:
- Llama 3.1 features 405 billion parameters, making it the largest open-source model.
- Updated 8B and 70B models offer improved performance and capabilities.
- Expanded context windows to 1208 tokens enhance handling of larger code bases.
Key Takeaways:
- The 405B model excels in reasoning, tool use, and multilinguality.
- New models support specific tool calls, improving code execution and mathematical reasoning.
- Developers can balance helpfulness with safety more effectively using the updated system.
Date: 2024-07-23 18:20 | Source: packetpushers.net
Summary:
Recent months have seen various Wi-Fi security vulnerabilities, including SSID confusion, RADIUS attacks, and critical Windows Wi-Fi driver flaws.
Main Points:
- SSID confusion exploits have emerged as significant threats.
- RADIUS attacks are increasingly targeting wireless networks.
- Critical vulnerabilities in Windows Wi-Fi drivers pose major security risks.
Key Takeaways:
- Wi-Fi security requires constant vigilance due to evolving threats.
- Understanding specific vulnerabilities helps in mitigating risks.
- Expert insights, like those from Stephen Orr, are valuable for navigating Wi-Fi security challenges.
Date: 2024-07-23 18:12 | Source: WorldofAI

Summary:
Meta AI's open-source Llama 3.1 model offers advanced capabilities, including multilingual support and complex reasoning, in 8B, 70B, and 405B parameters.
Main Points:
- Llama 3.1 model is available in 8B, 70B, and 405B parameters.
- Features include multilingual support, complex reasoning, and coding assistance.
- The 405B parameter model competes with top closed-source models.
Key Takeaways:
- Llama 3.1 is fully open-sourced and can be fine-tuned, distilled, and deployed anywhere.
- Integrates multiple plugins and applications for enhanced tool usage.
- Open-source model performance matches top benchmarks in coding and mathematics.
Date: 2024-07-23 17:19 | Source: techcrunch.com
Summary:
Digital banking startup Mercury has ceased serving customers in specific countries, including Ukraine, as informed to some founders.
Main Points:
- Mercury informed founders about service discontinuation.
- Certain countries, including Ukraine, are affected.
- The announcement impacts Mercury's international customer base.
Key Takeaways:
- Mercury's decision affects founders in impacted countries.
- Ukraine is explicitly mentioned among the affected regions.
- The change highlights challenges in international digital banking services.
Date: 2024-07-23 16:35 | Source: Cisco

Summary:
Danela from Cisco Wireless Tech explains the step-by-step process for renewing web administration and authentication certificates using a CSR on the controller.
Main Points:
- Navigate to configuration, security, and PKI management on the 9800 controller.
- Generate a new RSA key and create a certificate signing request (CSR).
- Save the generated CSR and note the trust point for chain validation.
Key Takeaways:
- The process works even in high availability deployments.
- Ensure the key is exportable and save the CSR securely.
- The trust point name is crucial for chain validation later.
Date: 2024-07-23 16:35 | Source: NetworkChuck

Summary:
I'm starting my journey to become a certified hacker with Hack The Box's penetration testing certification, documenting the entire process.
Main Points:
- Beginning path to earn Hack The Box certified penetration testing specialist certification.
- Partnering with Hack The Box to document the certification journey.
- Certification involves hacking real-world environments and performing actual penetration tests.
Key Takeaways:
- Hack The Box offers gamified hacking labs to keep skills sharp.
- Certification journey will be documented in a series of videos.
- Exam tests practical hacking skills in real-world scenarios.
Date: 2024-07-23 16:23 | Source: arstechnica.com
Summary:
Congress is concerned that a worker shortage could potentially delay necessary repairs for CrowdStrike's cybersecurity systems.
Main Points:
- Congress is worried about potential delays in cybersecurity repairs.
- A worker shortage is the primary cause of these potential delays.
- CrowdStrike's repairs are critical for maintaining cybersecurity.
Key Takeaways:
- Addressing the worker shortage is crucial to avoid delays in cybersecurity repairs.
- Ensuring timely repairs for CrowdStrike is essential for cybersecurity.
- Congressional concerns highlight the importance of workforce stability in cybersecurity maintenance.
Date: 2024-07-23 15:30 | Source: ByteByteGo

Summary:
This content explains session-based authentication and JSON Web Tokens (JWTs), detailing their mechanisms, pros, and cons for web authentication.
Main Points:
- Session-based authentication involves the server creating and storing session data.
- JSON Web Tokens (JWTs) are generated by the server upon valid credential verification.
- The choice between sessions and JWTs depends on specific application needs and infrastructure.
Key Takeaways:
- Session-based authentication allows easy session revocation by invalidating server-stored session data.
- Distributed systems using session-based authentication require a centralized session store for consistency.
- JSON Web Tokens (JWTs) offer a stateless authentication mechanism, reducing server-side storage demands.
Date: 2024-07-23 15:26 | Source: feeds.packetpushers.net
Summary:
The debate centers on whether enterprises should abandon Microsoft due to its numerous security vulnerabilities versus its strong integration and utility.
Main Points:
- Microsoft poses significant security risks due to numerous vulnerabilities and questionable responses.
- Despite security concerns, Microsoft's integration and utility in enterprise environments are highly attractive.
- Johna Till Johnson and John Burke discuss the challenges and considerations of potentially ditching Microsoft.
Key Takeaways:
- Enterprises must weigh the security risks against the benefits of Microsoft's strong integration.
- The decision to abandon Microsoft involves evaluating both its vulnerabilities and enterprise utility.
- Expert opinions highlight the complexity of deciding whether to continue using Microsoft.